NFC Security Bag including the NFC smartphone app for optimal tracking and storage with tamper protection – first look available at GPEC from September 9th – 11th 2014, Stand C67 in H1.
New release available now from ENAiKOON, NFC Security Bag and the coordinating NFC smartphone app with integration into inViu web, ENAiKOON’s highly secure telematics platform.
Typical use cases
Security bags with an integrated NFC tag are particularly suitable for the safe transport and professional storage and safekeeping of important objects, including tamper protection. The following are examples of typical use case for these security bags:
• Confidential and important document transfer
• Transport of high value goods
• Equipment security policy for weapons, illegal narcotics, and other restricted access items
• Transport of urine and blood samples for doping tests
• Chain of custody drug testing
• Forensic evidence collection and storage
• Personal property bags for patients in hospitals or deceased individuals
• Inmate personal property inventory
• Chain of custody for expensive or dangerous pharmaceutical, biological or chemical products
• Secure data disposal to verify the destruction or hard drives or other storage devices with important data from banks, power plants, and other facilities which are not connected to the internet
• and many more
Lost or altered items are now a thing of the past.
Typical requirements
• Error-free and 100% traceable documented tracking for transport of critical objects
• Complete documentation of the contents, storage area as well as the responsible person in each case for the NFC security bag
• Management of additional information as needed for each security bag including for example comments, photos, audio notes, videos, electronic signature capture, etc.
• Evidence of tampering, changing or tampering with the contents of the security bag are evident and able to be identified
Features of the NFC security bag
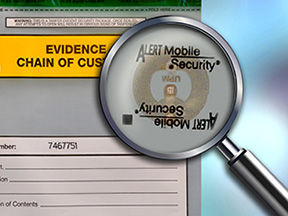
NFC tag for tamper proof identification
The high tech NFC security bags from ginstr are equipped with an NFC tag and are more secure than the current bags on the market using bar-codes or written information.
With the NFC tag the NFC security bag and the associated information is saved in a databank using a smartphone app. By simply reading the NFC tag an approved smartphone is able to access all relevant data concerning the associated NFC security bag.
In addition to the collecting and reading the NFC security bag information photos, videos, electronic signature capture, audio notes, comments, etc. can be centrally stored and recalled later.
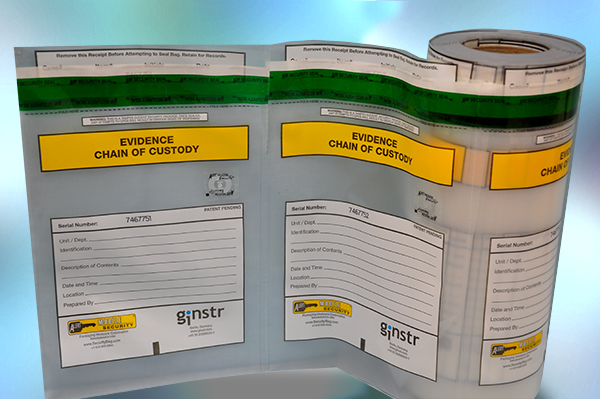
Consecutive serial numbers
In addition to NFC tags the NFC security bags have consecutive serial numbers that are tamper proof and stored on the NFC tag. The serial numbers are unique per customer and the NFC tags are globally unique. Thus, neither can a security bag be missed nor another organisations security bags used.
Tamper evident closure
The NFC security bag cannot be opened without destroying it. Attacks by heat, cold, or attempts to close a bag which has been opened are recognisable due to obvious signs of tampering.
Removable ownership receipt
With this record the owner of the contents can prove ownership or the sender of the bag that it is shipped.
Customisable printing
The NFC security bag can be printed with your logo and any additional fields as needed for your organisation.
A variety of sizes and optional extras
The NFC security bags can be produced in different sizes.
Standard sizes are 152×228 mm (6×9 inches), 228×304 mm (9×12 inches), 304 x457 mm (12×18 inches), 381×508 mm (15×20 inches)
The security bags can be produced in different versions, for example with an antistatic coating for hard drives and other storage devices.
Price
Depending on the quantity ordered the cost of NFC Security Bags ranges from €2.90 – €4.90 per unit. The monthly subscription fee for the use of the smartphone app and back end administration software, including data storage on ENAiKOON’s highly secure servers, costs €9.90 per month per user with a minimum contract length of 24 months. All prices are excluding VAT.
More information about prices
More informationen
Read more on the ginstr website about use cases and functions.